Statement
Do you know how to make a patch?
👉 Click to download the patch file
Objective
The goal of this challenge was to locate and analyze the functions inside the patch file to identify the routine responsible for generating the flag.
Solution
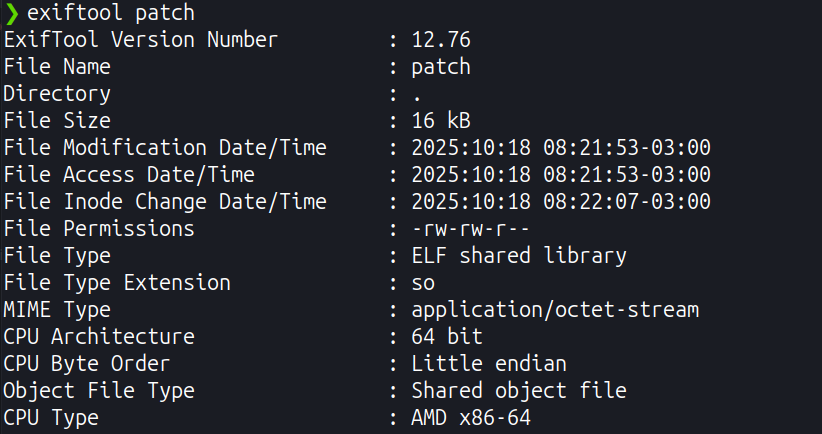
Metadata
I checked the binary’s metadata looking for hints or inconsistencies; I didn’t find anything relevant.
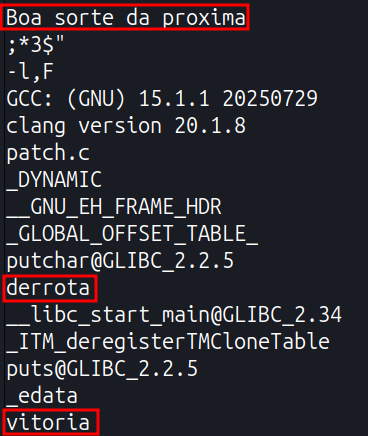
Readable strings
I listed all readable strings from the file searching for clues. I found a sentence and two words that didn’t point directly to the flag. The only obvious connection was between “defeat” and the string “Better luck next time”.
![]()
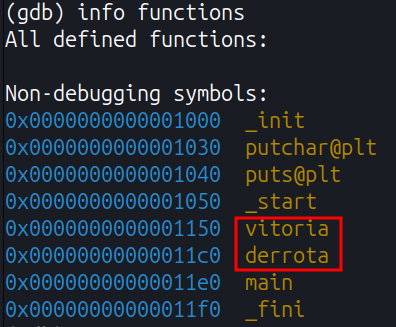
Checking the program’s functions
While reviewing the program’s functions, it became clear that the words found in the strings were part of the program flow. This suggested that the functions derrota() (defeat) and vitoria() (victory) would be relevant, and that vitoria() would likely return the flag.
![]()
Executing the functions
Initially, I tried running the functions in debug mode but received a permission error. After adjusting the permissions/environment (allowing debugging/execution), I was able to call the functions.
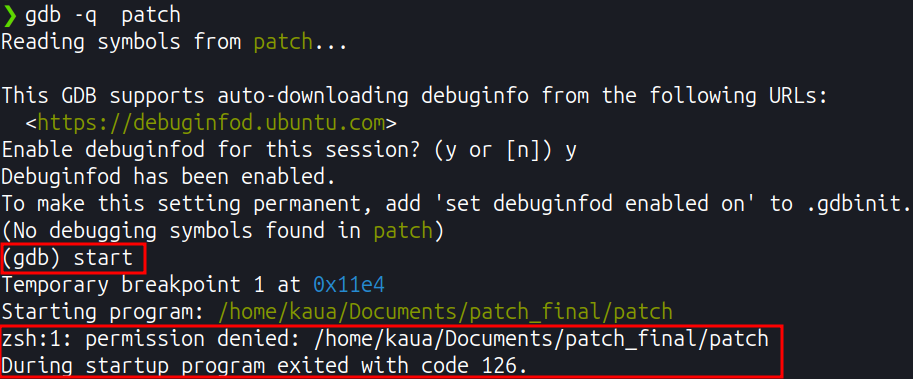
![]()
I had to deal with an unknown return type; to work around this, I treated the return as void temporarily to force execution. When running them:
derrota()printed the same sentence found in the readable strings;vitoria()returned the flag.
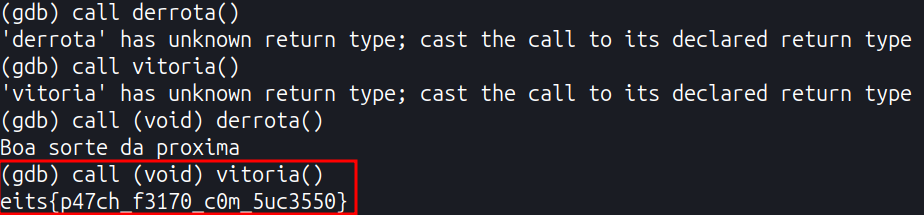
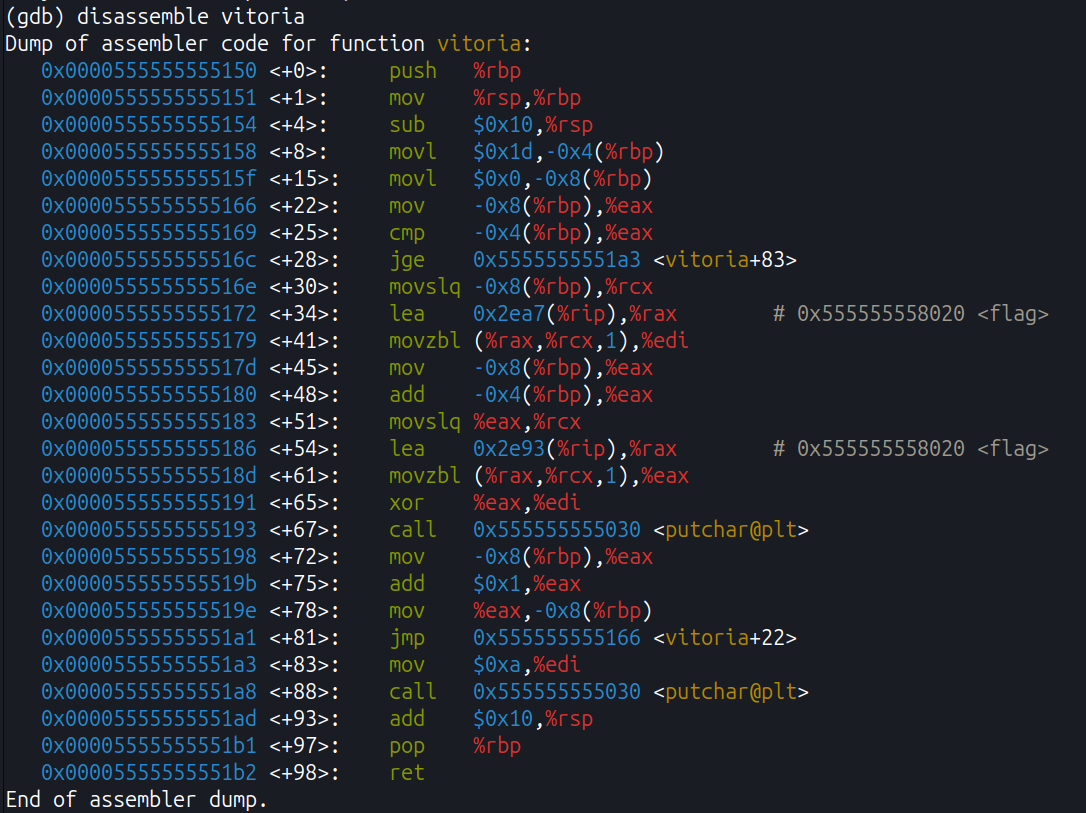
Interpretation / explanation
The function derrota() simply returns the raw string stored inside the binary, which is why it was already visible in the readable strings. The vitoria() function, however, appears to perform some decoding process on previously stored data; when this routine executes, the flag is revealed.