Objective
The goal of this challenge was to perform reconnaissance, analyze files (steganography/strings), decode credentials, and exploit a weak access control to achieve privilege escalation.
Solution
Performing reconnaissance
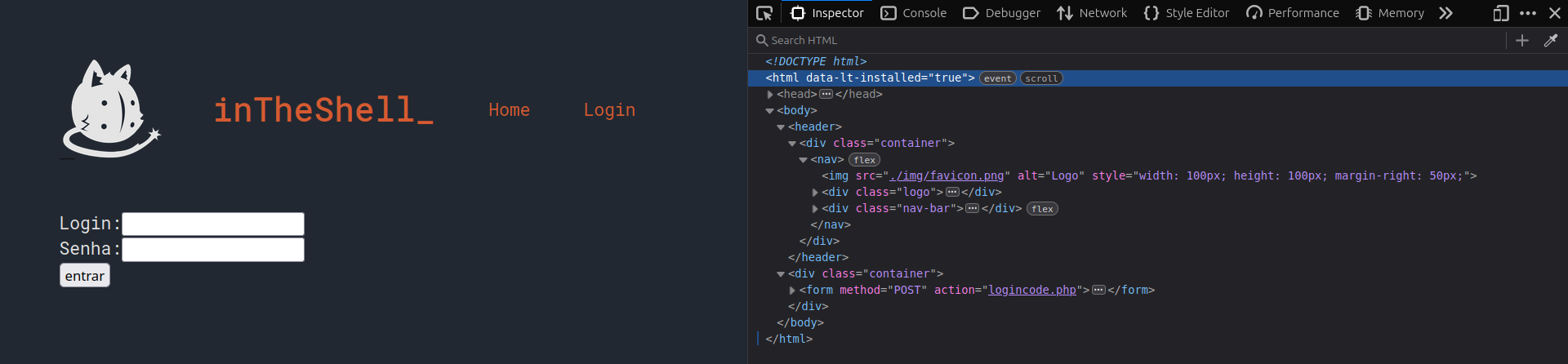
At first glance, the site contains only two tabs: Home and Login. The Home tab redirects to the Login tab. I inspected the HTML and the browser console, and nothing unusual appeared.
To test the login system, I started with a simple SQL Injection test: ' OR 1=1 --.
The system returned Incorrect username and/or password, suggesting there was no trivial SQL vulnerability in the login route.
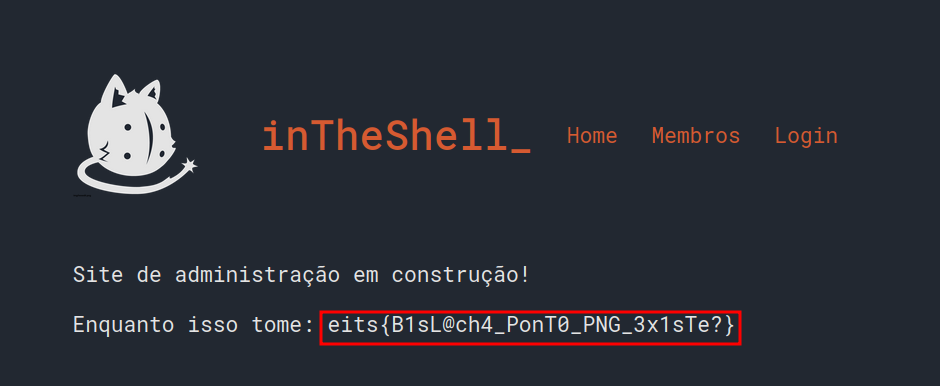
Looking more closely at the page, I noticed a small text on the logo:


This text pointed to a directory/file on the site that served an image.
Analyzing the image
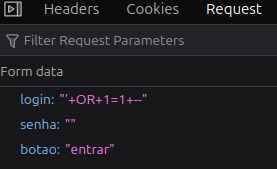
I downloaded the image and searched for readable strings (using strings). The image appeared to be a black background, but inside the strings I found data resembling encoded credentials.
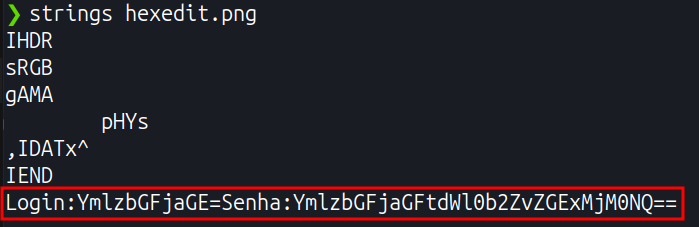
Returning to the login page, I tried the credentials found and clicked login, but again received Incorrect username and/or password.
Looking more carefully, it became clear that both the username and password were encoded in Base64 — a strong indicator being the = at the end.
Decoding both using CyberChef, we get:
- Username: bislacha
- Password: bislachamuitofoda12345
With the correct credentials, the login was now successful.
Access
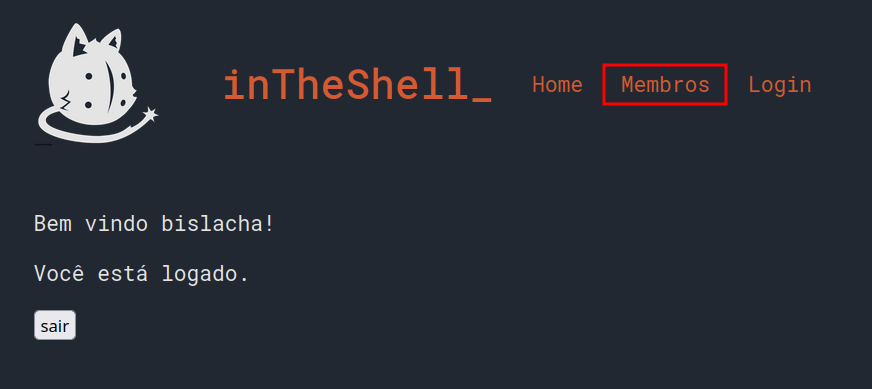
After logging in, a new tab called Members became available. There, I saw a list of current and former members; I focused on the authenticated user (Bislacha).
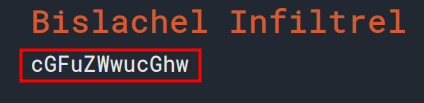
Instead of the nickname, we can see another Base64 string; decoding it yields: panel.php.
Panel.php
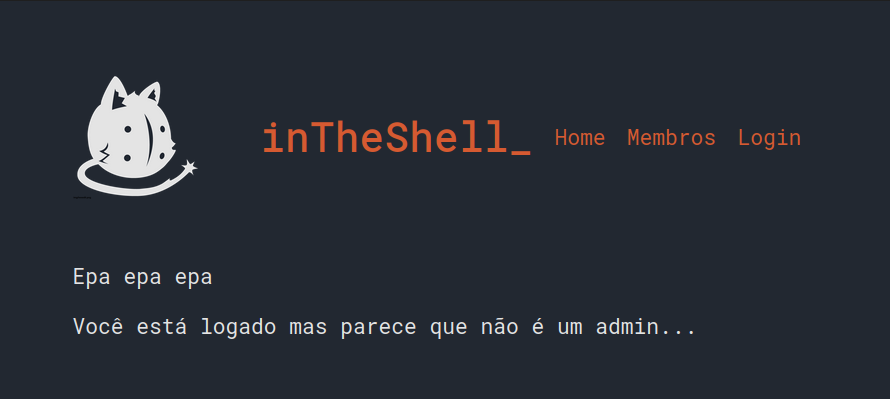
Accessing /panel.php, I was informed that the account was logged in but not an admin. This indicates that an administrative panel exists and is protected by access control — meaning privilege escalation was likely possible.
Privilege escalation
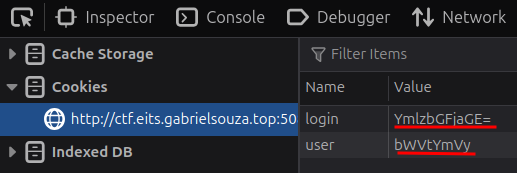
Inspecting the stored cookies, I found the fields login and user with their corresponding values. They were again Base64-encoded. Decoding them, we have:
- login: bislacha
- user: member
Since the system stores user roles in Base64 and we need to escalate to admin, I replaced the current user value with YWRtaW4= (the Base64 for admin) and refreshed the page.
After refreshing the page, the interface switched to the administrator version, and the challenge flag was displayed.